When Ransomware Hits, Will Your EHR Survive?
Healthcare is the most attacked industry in the world. Ransomware groups target EHR specifically because it is the most critical system your health system runs. CloudWave built an assessment to tell you exactly how prepared you are to recover it.
The Threat
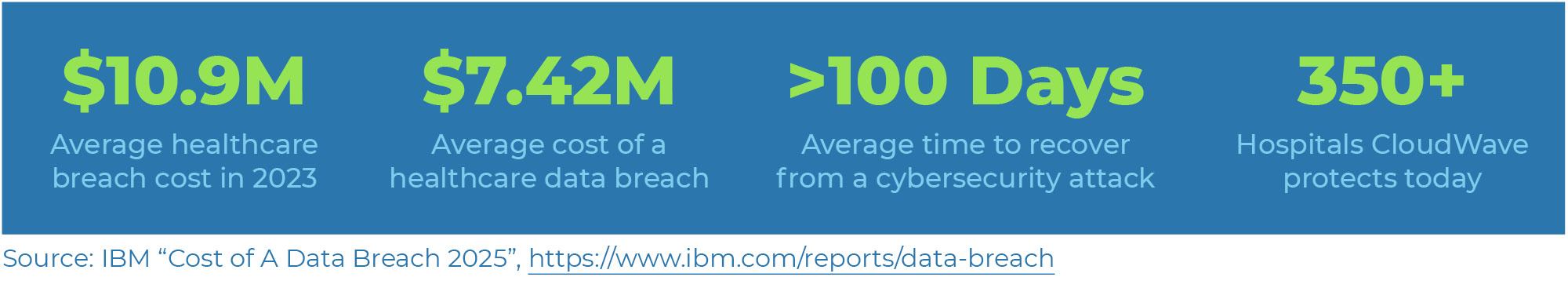
Healthcare has topped the list of most-breached industries for 13 consecutive years. Epic runs clinical operations for more than 305 million patients in the United States. When Epic goes down, care delivery stops.
Ransomware groups study your environment for weeks before they act. They go after backup systems first. By the time you know you have a problem, your recovery options are already damaged.
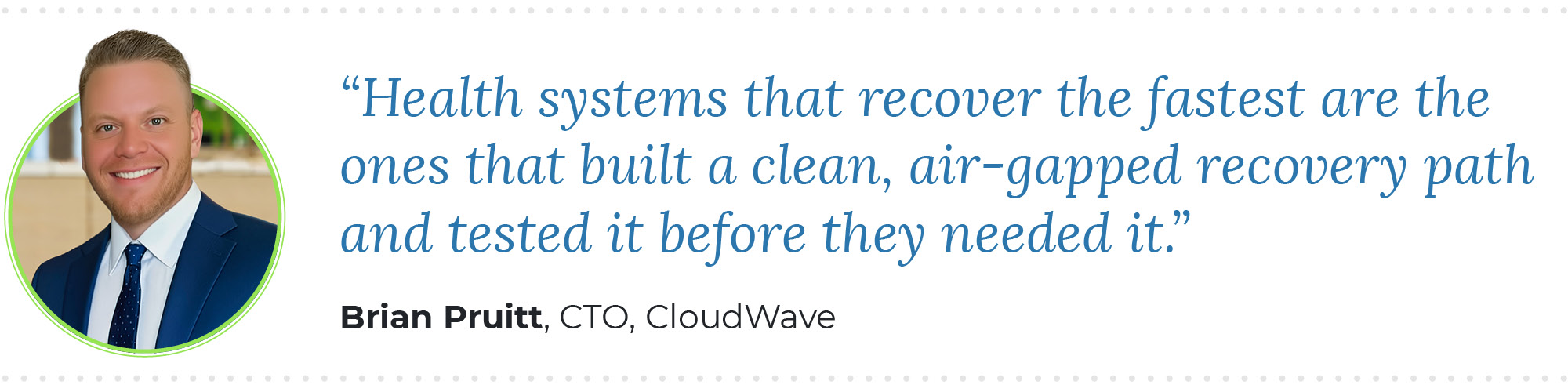
The question is not whether your organization will face an attack. The question is whether you have a clean, certified path to restore Epic, and how fast you do it.
Attackers Target Backups First
Before detonating ransomware, threat actors corrupt your backup systems. That way, when you reach for your recovery options, they are already gone.
Downtime Has Patient Safety Consequences
Health systems lose an average of $1.27M per day during EHR downtime. Peer-reviewed research links prolonged Epic outages directly to increased patient mortality rates.
Integrated Systems Multiply Exposure
Epic’s Interconnect APIs, third-party connections, and hybrid environments create a large attack surface. A single point-in-time security review will not catch all of it.
Regulators Are Paying Attention
CMS, OCR, and state attorneys general have increased scrutiny of health system cybersecurity after breaches. Your board needs documented evidence of a defensible recovery posture.
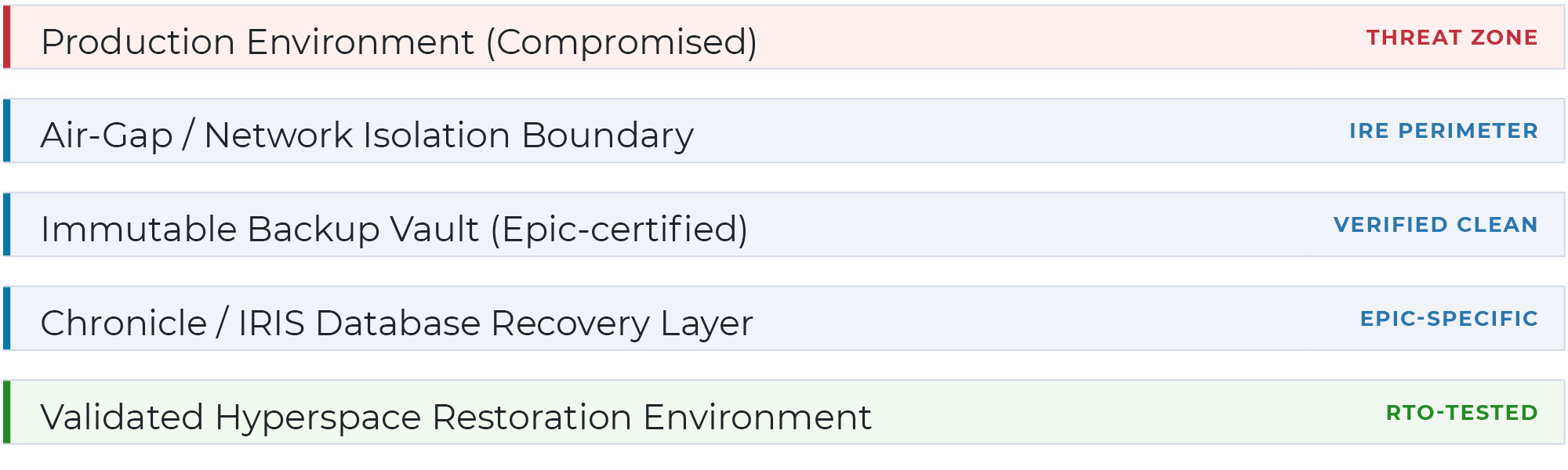
What Is an Isolated Recovery Environment?
An Isolated Recovery Environment (IRE) is a hardened, air-gapped infrastructure zone built to restore Epic even after your primary environment and standard backups have been compromised. It is your last defensible recovery option.
Epic has formalized IRE requirements and built a certification framework around them. Your IRE must meet Epic’s specific technical specifications: Chronicle database integrity, hyperspace environment validation, Interconnect service restoration sequencing, and Cache/IRIS layer recovery. General cybersecurity architecture does not satisfy these requirements.
CloudWave has operated Epic hosting environments for over 300 hospitals for more than two decades. We assess IRE readiness from an operator’s perspective, not a generalist consultant’s point of view.
IRE Architecture: Layer by Layer
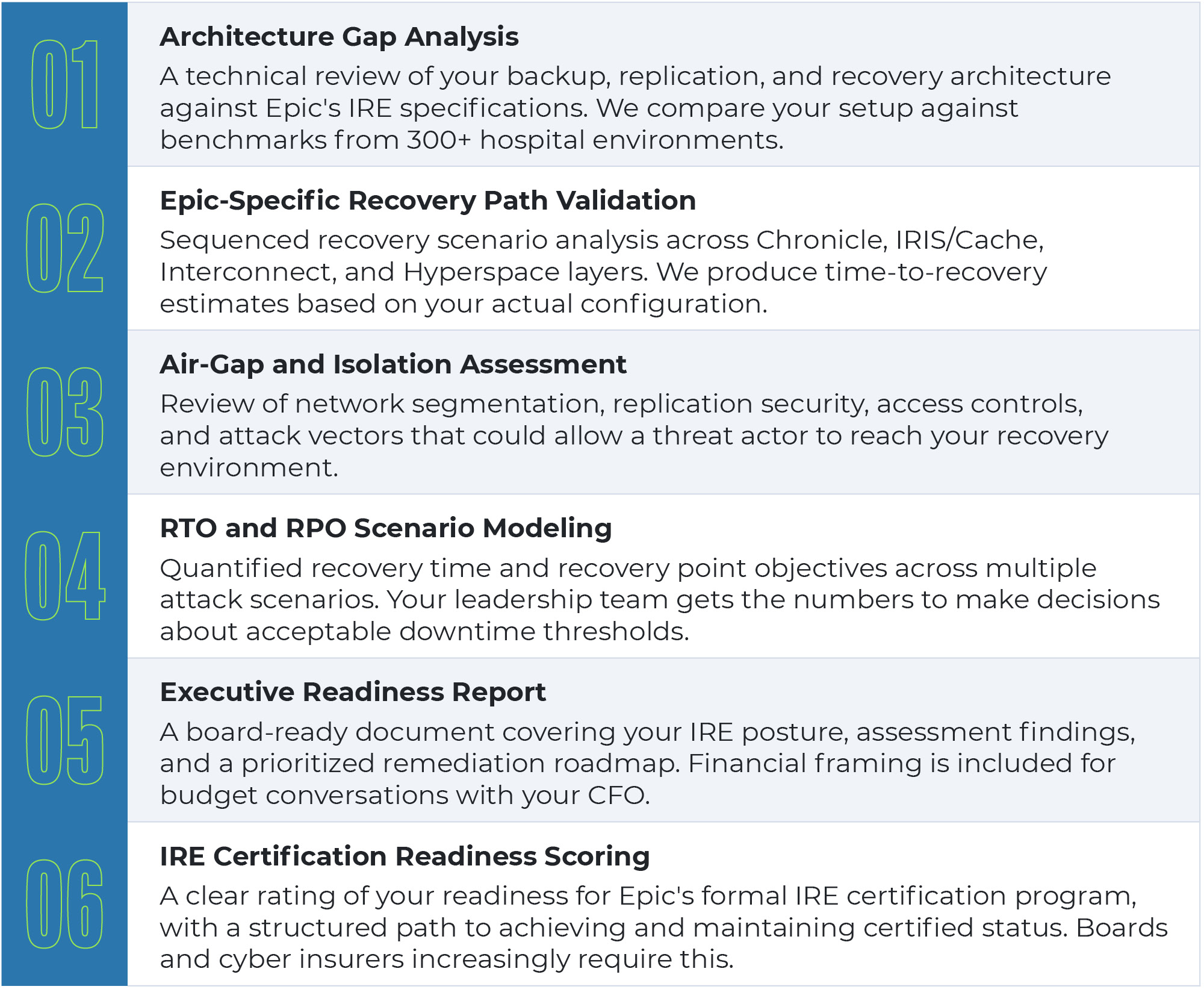
The CloudWave Epic IRE Assessment
This is not a checklist review. Our engineers build and operate EHR hosting environments at scale. They conduct a technical assessment of your specific environment and produce a report your board, cyber insurer, and regulators will accept.